29th Apr 2024
Azraf Al Monzim
u/monzim
IUT 11th National ICT Fest OpenAPI Hackathon Team DevSprint's Solution for the Preliminary Round
My team DevSprint has earned a place in the Preliminary Round of the IUT National ICT Fest OpenApi Hackathon, emerging from a pool of over 55 teams. Among them, only 10 were chosen to advance. We're excited to announce our invitation to the final round, taking place on April 26th and 27th. In this blog post, I'll be unveiling our solution for the preliminary round.
Question-1
Your younger brother Tony Stark has given his SSC exam in February this year. The result is going to be published in May. Now, a lot of students along with your younger brother will try to access the website to see the result. As a result, the server might fail to respond properly. Your younger brother is tense about getting the result. He is trying again and again but can’t enter into the website for huge traffic.
As a developer and a caring brother, can you find a way out to help your brother to know the result when it’s available?
Bonus: Now imagine the other side of the coin. The developer of the ssc result system. noticed that some brilliant developers like you found a way to bypass the result system.They hire you to give a solution to prevent bypassing the result system. What you will do now
Solution
i) As a brother, We can get an IP Address and find out the zone and if there is any service for this zone we can connect using vpn for this.
ii) As a developer:
-
If it is a monolithic system, We can create multiple instances of that backend system and load balancing them.
-
Make it serverless we can use like AWS lambda, Azure function or Cloudflare workers
-
Implementing Caching
II) BONUS:
-
Although someone bypasses the system, so that we can say there are security bugs, there are no authorization systems implemented or else the Authorization system is not secure enough to handle this exception.
-
First of all we can implement a recaptcha system to prevent bot activity, multiple requests at the same time from the same device.
-
For better DDOS protection we can use cloud-flare
-
We can implement a rate system in our backend server.
-
We can use more robust authentication systems, for example JWT based authentication systems. Also RBAC (Role Based Access Control) so that those who have access to that particular resource, he/she can access that particular resource.
-
We will use HTTPS Protocol to communicate with server
-
We can also use dedicated firewall to prevent UnAuthorize attempts
-
Implementing Logging system our backend server so that we can monitor logs for any suspicious activity.
Question 2:
You are a software developer tasked with integrating third-party APIs into a stock prediction application. You have a third party stock exchange API that provides various parameters related to the stock exchange, some of which are updated in real-time while others are updated infrequently. You can also introduce some new metrics with the help of some calculation. You are charged from that third party by per api calls in a day.
Your application can greatly influence the accuracy of stock predictions and help users determine whether they should invest in a particular stock or not.
When integrating and consuming these types of third-party APIs, what are the key factors you should keep in mind?
Solution:
-
First of all, we have to keep in mind that we need to minimize api calls to minimize api cost.
- We will not do unnecessary api calls
- Implement caching (on Frequently access data)
-
make sure that we are handling errors properly. We need to implement a feature to retrieve api call is there is any exception found.
-
We will implement our own real-time database. It can be a firebase realtime database, supabase, aws dynamo db or any other database that support real time communication. [ We are going to save the realtime data in our own database and we will use that data to make predictions. We can use websockets to get the real-time data from the third-party API and update our database. This way we can reduce the number of API calls we need to make and also have more control over the data ]
-
We will not call the third party api from the client device rather the api will always call from our backend system.
-
We will make sure that the third party api KEY remains secure. Always use HTTPS.
Question 3:
You are a software engineer working for a gaming company tasked with developing a multiplayer chess game. The game aims to provide players with the ability to compete against each other in real-time, even if they are using different devices and are located remotely from each other. One day, you receive a new project assignment: implement the real-time movement update feature for the chess game. Your goal is to ensure that when one player makes a move, it is instantly reflected on the opponent's device without any delay, providing a seamless and synchronized gaming experience.
Describe the technical approach you would take to ensure synchronized movement updates between both devices in real-time using webRTC or socket-based communication.
For example there are also some chess tutorial features where you can learn chess from chess experts. There may be video feeds of the instructor and of you and real time chess movement.
Solutions:
-
WebRTC For the real time video and audio streaming (Tutorial Feature):
Here we are going to use WebRTC. WebRTC can make a peer-to-peer connection between the two devices without needing a central server. And It will allow us to send video and audio streams between the two devices in real time. Because the data is sent directly between the two devices, it will reduce the latency and provide a better user experience for video. It will be a better option because video bitrate is high and it will be better to send it directly between the two devices. -
Realtime Chess Movement: Because chess moves need to be validated by the server and then sent to the opponent. We can use socket-based communication to send the chess movement data between the two devices. Because websocket have a middleman server so the server can manipulate data (checking suspicious checking protection and other validation) before doing any communication between two devices. Also is a full-duplex communication protocol, it will allow us to send data between the two devices in real-time. For that we can use solutions like AWS API Gateway, AWS Lambda, AWS DynamoDB. We can use AWS API Gateway to create a websocket connection between the two devices. We can use AWS Lambda to validate the chess movement data and send it to the opponent. We can use AWS DynamoDB to store the chess movement data and send it to the opponent.
Question 4:
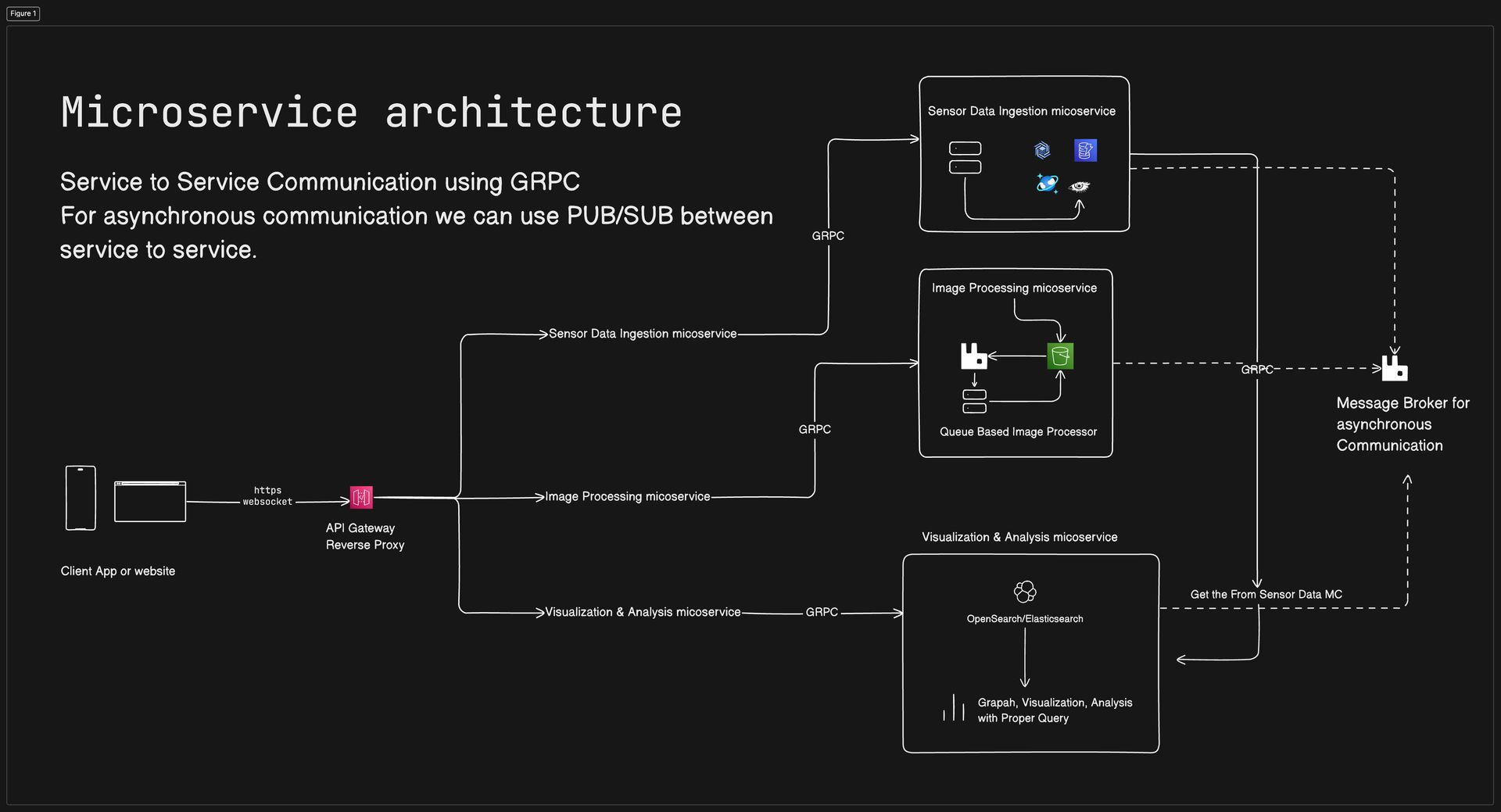
You are a software architect tasked with developing a comprehensive application for the agriculture domain. The application aims to leverage various technologies, including sensors, IoT devices, computational tasks like image processing, real time data visualization, and analysis, to provide farmers with valuable insights and tools to optimize their farming practices. There may be different instruments like drone, irrigation pump, utility machines etc integrated with the system
Imagine you're working with a team of developers, agronomists, and domain experts. Your goal is to design an application that seamlessly integrates data from sensors and IoT devices deployed across farmland, processes this data , and presents actionable insights to farmers through intuitive data visualization and analysis tools.
Your task involves devising a robust architectural plan to make this application.How will you design such a system?
[As part of your response, feel free to include diagrams illustrating the proposed architecture, data flow, and component interactions to provide a visual representation of your design.]
Solution:
Diagram: https://app.eraser.io/workspace/pNgmrl7nmlRABw4Zjim0?elements=i1dJ4YCyCcUXphzDHxSGIg
Question 5:
You are leading a development team comprising seven members, each specializing in different roles: two frontend developers, two backend developers, one DevOps engineer, one QA tester, and one product manager.
Given the diverse skill sets and responsibilities within your team, you need to establish an efficient workflow and version control system to facilitate collaboration and code management.
Your first step is to create a Git repository for the project and define the guidelines and best practices for its usage.
Solution:
Our guideline will be look like this:
-
Create a git repo for this we are going to using Github ( Cause it have better CI/CD support Github Action )
-
We use proper coding practice and a linting system and an automatic CI system will check the code while a developer pushes new code in the repo.
-
Proper use of Branch for dev and production.
-
Follow proper commit message we can create some rules for commit message also
-
We will also test the code so that everything is working fine. We will use automatic testing system using Github Action workflows
-
We can use Github Project for issue tracking and management
-
Proper Documentation using Github Readme
-
Semantic Versioning for project
-
Proper access control using git
Question 6:
You work for a telecommunications company where there's been a noticeable uptick in fraudulent calls powered by scammers.Scammers sometimes used ai based voice too. These calls are not only disruptive but also pose serious risks to customers who might unknowingly divulge sensitive information to scammers.
As part of your role, you are tasked with devising a strategy to prevent and mitigate the impact of fraudulent calls. Your goal is to implement measures that safeguard the integrity of the communication network and protect customers from potential harm. You can use any AI based api that is available as your reference
Solution:
Data Collection and Analysis: We will record every call and generate a transcript (We can use WS Transcribe or Azure Speech Services to convert incoming calls to text). To detect a number can be a spammer we can use api from Truecaller or some other api service from aws or azure marketplace
Voice Analysis: We can use AWS Rekognition or Azure Cognitive Services to detect any AI Generated voice or detect any scamming pattern from the recorded voice and transcript. We can also use these services to detect unusual conversational patterns to mark a call as scammer. BLOCK already scammed phone numbers.
Educate Customer: will run some social activity to educate customers about scammer calls and scamming patterns. So that they can know when someone is trying to scam them. Also a custom customer feedback feature to know if a call is a scam or not. And use these data to update the accuracy of our scam detection AI model.
Question 7:
Your team develops an awesome web app. Recently, users have reported experiencing delays in receiving responses from the system, with response times averaging around one minute.
As this delay can stem from various underlying issues, you are tasked with finding the problem and how it can be resolved. Different members of the team may have different views on that issue. If so, write all of them
Solution:
We think the main issue is in this case in the backend. So we can do this to solve the delay issues:
-
If the traffic is big and the server can not handle the load we can scale the server horizontally if it is not a monolithic system. If so we can scale the server vertically to handle more requests at a time. If possible, shift some api’s to serverless systems like lambda or Azure function type. SO THE DEVOPS ENGINEER WILL MAKE SURE THE SYSTEM SCALABILITY.
-
Check the db log for the query if it is the problem from the query then we can create indexes for better query. Also we implement caching for frequently used (unchanged) data for this we can use like in memory db like Redis, MemcacheDB, KeyDB etc. BACKEND ENGINEER WILL ENSURE THIS
-
We can implement CDN for content caching. THE DEVOPS ENGINEER WILL ENSURE THIS
-
From the frontend site we can do client side caching and make sure our site is fast. We can use modern web frameworks like Next.js, Remix for better web experience. FRONTEND ENGINEER WILL ENSURE THIS
-
Do more and testing to detect issues. QA ENGINEER WILL ENSURE THIS. and developer will solve this.
Question 8:
You are a CTO of a well known software company. A big client wants to create an application to promote yoga and physical fitness among older adults. The application aims to provide a user-friendly platform that enables senior citizens to access guided yoga sessions, fitness routines, and wellness resources tailored to their needs and preferences.
You have to work closely with a team of designers, developers, and wellness experts to develop an application specifically designed for elderly people interested in yoga and physical fitness. The goal of the application is to provide an intuitive and visually appealing user experience that caters to the unique needs and preferences of elderly users. The system may need to use AR/VR technology
You have to make a proper plan to win the project from that big client. Which factors will you and your team keep in mind?
Solution:
Yoga is like an exercise system that's been around for a long time. Lots of grown-ups everywhere enjoy it because it helps them in many ways. We are very happy and interested to work with this project and bring some impact for the adults' health. Below are the factors which we will keep in mind to develop this great App.
-
User Research: First of all we will, Conduct in-depth user research with senior citizens throughout the survey to understand their:
-
preferred forms of yoga and fitness objectives.
-
Comfort level and experience with technology.
-
Physical disabilities (limitations and capabilities)
-
Accessibility needs (vision, hearing, dexterity).
-
Competitive analysis: Examine the fitness applications that are currently available for seniors, noting their advantages, disadvantages, and areas for improvement.
Developing a Winning Proposal:
-
What we will Focus on User Experience (UX):
-
Physical disabilities (limitations and capabilities)
-
Create a user interface (UI) that is straightforward and easy to use, with big, obvious buttons, obvious navigation, and simple, minimalistic design features. Employ well-known analogies and stay away from intricate movements or exchanges.
-
Yoga Tutorial Platform:
-
Forming Strategic Alliances with Certified Yoga Teachers Will Help Build an Extensive Collection of Senior-Specific Yoga Practices.
-
To carefully select educational resources which highlight the benefits of yoga for the prompt of healthy aging, personalized fitness programmes should be offered that are adapted to each individual's personal needs and preferences.
-
Accessibility:
-
To ensure an inclusive and user-friendly experience for the visually impaired, we will enhance accessibility for all users with features such as voice narration font sizes, high contrast themes and font sizes that can be adjusted. Check out the possibility of allowing users to monitor their progress easily with a wearable Health Tracker compatible device.
-
Community:
-
Incorporate social interaction features like group lessons or chat events to combat isolation.
-
Explore AR/VR technology for yoga experiences that foster community awareness and empowerment.
-
Building a Powerful Team:
-
Formulate a Comprehensive Team Comprising UX/UI Designers, Accessibility Experts, Senior Fitness Yoga Instructors, and Gerontologists to Drive Informed Design Choices.
-
Initiate Prototyping and User Testing Phases to Solicit Early User Input, Enabling Iterative Design Enhancements.
-
Strategize for Scalability and Future Expansion by Outlining Development Plans, Including Potential Integrations with Smart Home Devices to Facilitate Health Monitoring.
-
Presentation:
-
Customize your solution to align closely with the client's requirements, emphasizing how the program directly addresses their targeted objectives.
-
Highlight the user-centric approach embedded within your team's skill set and expertise.
-
Present a functional prototype showcasing fundamental features, underscoring your dedication to delivering a user-friendly experience.
Question 9:
Imagine you got a team at a software company specializing in API solutions. Your team has developed a powerful API that offers valuable functionality and services to potential customers. Now you want to sell your API as a third party API service.
What things will your team keep in mind while developing such an API that you can sell in the market? What will be your strategies to sell the API in the market?
Solution:
-
We need to make sure the system can handle millions and millions of requests so we need to make a scalable system that can be easily scalable and distributed. For this we can follow Microservice architecture or event driven architecture to make the system. We can use Kubernetes to deploy this distributed system and scale as our needs in future.
-
We need to make sure proper standard documentation of the api. We can use like OpenAPI Specification for api documentation or SWAGGER like tools to generate api automatically
-
Api versioning. We need to make sure proper api versioning like /v1, /v2 for apis
-
Implementation of Caching
-
RATE LIMIT
-
Authentication and authorization for api and API KEYS for users
-
Logging and Monitoring the api use to calculate cost
-
Api KEY invalidation system
-
Customer feedback to improve the api’s
Question 10:
You're a software engineer working on a team responsible for developing an API for an e-commerce website. The API plays a crucial role in facilitating transactions, managing inventory, and providing real-time updates on product availability. With the e-commerce website rapidly rolling out new functionalities to stay competitive, there's increasing pressure to deliver high-quality code in less time. However, this rush has led to an uptick in errors stemming from code changes.
Given the fast-paced environment with frequent code updates and a higher incidence of errors, what strategies can your team take?
Solution:
Implementing CI/CD pipeline
-
We can Implement Continuous Integration and Continuous Deployment in our code base to release new updates and check for code quality and testing.
-
We can do test driver development where each functionality needs to pass all the tests before rolling it to the production. In this case we are going to use github action workflows in our CI pipeline to check the code quality and make sure it is bug free.
-
Proper code review before merging it into the production branch. To merge it to the branch it needs to pass all the test and code standards that our linting system uses.
-
Proper rollback solution if any error occurs we can go back to the previous version. We can use multiple stages to check the code before it rolls out in production.
-
System monitoring and logging
Question 11:
You're developing an application with a registration form that requires users to provide their email and phone number. However, the client has specified that they don't want any form of email verification or phone number OTP verification as it may hamper smooth user experience. Additionally, the API used for this registration process is publicly available.
Given these constraints, what steps would you take to enhance the security of the API endpoint used for registration while still meeting the client's requirements?
Solution:
-
Implementing Rate Limit system per ip and device base
-
Use robust password to better security
-
Adding honeypot fields for bots
-
Use CROS
-
Client side validation for input fields
-
Monitoring the system and logs
-
Account blocking system
-
Store the password as encrypted
-
Educate the client about why we need proper security checks like email verification, or MFA
-
API Key authentication from the client
Question 12:
You've developed an API that serves data to both mobile and web applications. Initially, the response structure for mobile and web was different to accommodate the specific needs of each platform. However, over time, you've realized that there's a need to make changes to the response structure for making a better system. Also assume that your api may be consumed by others in future
When designing APIs that serve multiple platforms with potentially different response structures, what considerations should you keep in mind to ensure flexibility, scalability, and ease of maintenance when making changes to the response structure in the future?
Solution:
-
Proper api versioning
-
Make sure the new structure is compatible with the old version. If we can not make sure compatibility then we make sure to properly communicate properly with the team to resolve the issue. And Make sure before migration the old version works as well.
-
Documentation like OpenApi or Swagger.
-
Future proofing the apis
Question 13:
Imagine you're tasked with migrating data from your current application to a new system or cluster. This could involve transferring a large amount of data while ensuring data integrity, consistency, cost efficiency and minimal downtime.
Given this scenario, what steps would you take to successfully migrate the data from your current application to a new system or cluster? What considerations would you keep in mind to ensure a smooth and efficient migration process?
Solution:
Planning & analysis: make Proper plan about the migration of the data. If it is possible to migrate the whole data with every small downtime we can migrate in that way. If not then we can slowly migrate the data. For this we can follow the similar approach that discord takes while migrating their data from Discord Migrates Trillions of Messages from Cassandra to ScyllaDB approach.
-
First we will make sure migrate the whole data from one db to another while writing the new db in the old system and also in the new system
-
After all the old data is migrated in the new system then we will shift the write and read to the new system in this way we can migrate the whole data without any downtime
-
Use proper tool to make the migration is cost efficient and not affect the business
-
We will have make sure proper rollback and backup system in case something is happened
Question 14:
Imagine you're responsible for managing a hospital management system that caters to various roles such as doctors, nurses, patients, and receptionists. Each role has different permissions and access levels within the system.
Given this scenario, what strategies or techniques would you employ to implement a role-based access control system in the hospital management system? How would you define the roles, permissions, and access levels for each user category to ensure smooth operation and data security within the system?
Solution:
-
RBAC for Hospital Management System:
-
Roles: Doctor, NUrse, Patient, Receptionist.
-
Permission: Define actions for each role READ, WRITE, UPDATE, EDIT, DELETE, VIEW
-
Access Level: control within roles so that we can make sure only the user needs to access the data can access it. (ex: senior doctor vs resident doctor)
- Data Sensitivity: Restrict access based on data sensitivity
Implementation:
-
Assign roles during user creation. We can use the role while the user is accessing something. And check the appropriate role.
-
Map roles to permissions and access level
-
Strong authentication
-
Proper logging and monitoring system
While a user tries to access any data we will check the role for accessing the data if the user has the specific permission then he can access the data. In this way the system will be more secure and robust.
Question 15:
Write your thoughts on scaling and load balancing of the website for the scenarios given below:
1. Integrated Budget and Accounting System (IBAS), which serves as the central control hub for the Bangladesh Government. Employees from all around the country use IBAS at different hours of the day. Also, it remains closed during midnight
2. With the approaching festival season like Eid or Durgapuja, there's a significant surge in the number of people accessing the railway website to book tickets. This sudden influx creates a high load on the website infrastructure, resulting in potential performance issues and user frustration.
3. A friend group of three college students develops a software application for communication within their college community. However, the software unexpectedly gained immense popularity, attracting a large number of users who attempted to access it simultaneously. At first the number of users was 50, then 100, then 1000 and the numbers just gradually increased. This sudden surge in traffic puts significant strain on the software infrastructure, causing performance issues and downtime.
4. Consider yourself as a developer of a popular social media application like facebook, which is accessed from all over the world, from different geographical locations, at different hours of day and night. At some hours, the traffic may be very high.
Solution:
-
Case 1 (IBAS):
-
Vertical Scaling (Add more resource) the app during peak hour
-
Horizontal Scaling (Add more server) for long-term scalability
-
Case 2 (Festival Season Rail ticket)
-
Auto Scaling: Scale resources based on predefined metrics like traffic/CU.
-
Pre provisioning Resource: add temporary servers for peak hours
-
Load Balancing Essential to distribute traffic during peak times
-
Case 3 (College Social Networking App):
-
Horizontal Scaling the app
-
Loading Balancing
-
Case 4 ( Social Media)
-
Horizontal Scaling and Distributed the system in different region
-
Loading Balancing
-
Adding CDN for get better first content loading
Question 16:
You've been assigned the task of developing the backend database system for an e-commerce website that manages a substantial volume of data related to buyers, sellers, products, shops, and product categories.
Considering the complexity and scale of the e-commerce platform, how would you design the database? Or Furthermore, how would you design the database schema to effectively organize and manage data pertaining to buyers, sellers, products, shops, and product categories? Also write the api endpoints name you have in your mind
Feel free to leverage any communication technology, such as REST, GraphQL, RPC, gRPC, or a combination thereof, as well as any database type, including NoSQL, relational SQL, key-value databases,graph database, column database etc or a mixture of these.
Solution:
Database Selection:
-
Because it is an ecommerce site and product and its categories are related with one another we can use SQL support databases like (Postgres, CockroachDB, RDS etc), for Product and Category.
-
For various user info we are going to use NoSQL db like Cassandra, Dynamodb or Azure cosmos db ect.
In this senior i will use CockroachDB and Cassandra and for caching REDIS
Tables:
-
Products
-
Shops (owned by a user)
-
Product Categories (hierarchical structure possible)
-
Orders (with order items)
-
Carts (with cart items)
-
Reviews (by users on products)
-
User (Cassandra Table)
-
... (other tables as needed)
Relationships:
-
Users can have many Orders and Carts.
-
Orders and Carts contain many Order Items and Cart Items respectively.
-
Order Items and Cart Items reference Products.
-
Products belong to a Shop and a Category (or multiple categories).
-
Users can write Reviews for Products.
System Architecture:
We are going to follow microservice Architecture for this project. It will make sure the system is scalable and maintainable part by part and distributed. We can use individual databases per service need.
-
Service to Service Communication Direct communication if needed: GRPC (faster and type safe)
-
Api Gateway to the service discovery GRPC
-
Message broker like RabbitMQ or Kafka for interservice asynchronous communication
-
JWT based Authentication and AUTHORIZATION system. We can add ROLE in the JWT token for reduce db call while checking authorization
Because it will be a microservice in future we can add more features to the system easily.
Probable API Endpoints (REST):
User Management:
-
POST /users (Create user)
-
GET /users/:id (Get user details)
-
PUT /users/:id (Update user details)
Product Management:
-
POST /products (Create product)
-
GET /products (Get all products)
-
GET /products/:id (Get product details)
-
PUT /products/:id (Update product details)
Shop Management:
-
POST /shops (Create shop)
-
GET /shops (Get all shops)
-
GET /shops/:id (Get shop details)
-
PUT /shops/:id (Update shop details)
Order Management:
-
POST /orders (Create order)
-
GET /orders (Get user's orders)
-
GET /orders/:id (Get order details)
Cart Management:
-
POST /carts (Create cart)
-
GET /carts/:id (Get cart details)
-
PUT /carts/:id/add (Add item to cart)
-
PUT /carts/:id/remove (Remove item from cart)
Product Category Management:
-
POST /categories (Create category)
-
GET /categories (Get all categories)
-
GET /categories/:id (Get category details)
-
PUT /categories/:id (Update category details)
Review Management:
-
POST /products/:product_id/reviews (Create review)
-
GET /products/:product_id/reviews (Get product reviews)
We can use kubernetes to make sure the system is scalable and distributed.
Team DevSprint: UIU